 NetOps and Cyber SA in the Field
NetOps and Cyber SA in the Field
Meanwhile, the setup and management of deployed military networks becomes more complex as they leverage mature commercial enterprise technologies, and in some cases even use unsecured in-country cellular and telecommunication systems. It often takes days to get a battlefield network up and running, but U.S. Army leaders believe that in future operating environments, against a peer threat, forces will have to move on an hourly basis.

Stationary bases like those established in Iraq and Afghanistan won’t meet requirements. What’s more, warfighters need Cyber Situational Awareness (SA) capabilities that deliver comprehensive information about the status of the network and the digital ecosystem it supports. Battlefield networking is a mission-critical service, but cyber is now a contested domain. Commanders rely on the network for visibility into all facets of battle, so networking programs must ensure network availability and defense against cyber attack.
The goal for next generation Army command posts programs is for networks to be powered up and receiving live feeds in five minutes. Wireless networking capabilities will be key to meeting this goal, making it possible to set up and tear down the network in only minutes, instead of hours or days after warfighters establish operations in a new location. The simplification of battlefield information technology (IT) and cybersecurity will be essential so that lightly trained personnel can rapidly set up a network in the field. Likewise, network management must be simplified to ensure that the battlefield network stays up and running and commanders have a single, clear view of the network’s health and status at all times.
Gaps in understanding tactical network architecture, network status, cyber posture, and the spectrum/EW environment can hamper a commander's ability to make fully informed decisions at the tactical edge. U.S. DoD must retool its management of network, communications, and spectrum to maintain tactical overmatch in the cyber warfighting domain. Programs advancing concepts such as Joint All Domain Command and Control (JADC2) and Cyber Situational Understanding are beginning pilots to address subsets of well-known challenges in these spaces. The complexity of gathering and fusing data from multiple sources — particularly in disconnected, intermittent and limited (DIL) environments — necessitates progressing towards the ultimate vision of a unified network, one step at a time.
Today, tactical programs have a critical need for Cyber SA across defense information systems. Cyber SA enables cyber professionals and decision makers to gain a clearer picture of what is happening across DoD networks, and ultimately, a bird’s-eye view of the entire digital ecosystem. Network operations (NetOps) encompasses not only Cyber SA, but also a broader operational framework that includes network planning, management, configuration, and monitoring to operate, manage, and defend defense networks.
Tactical NetOps programs can play a key role in enabling mission success for warfighting in the cyber domain. They have access to the network architecture, network health data, and the 'pipes' to distribute that data to commanders wherever they are. Advances in NetOps tools hold the key to providing understanding in the cyber domain, enabling commanders in the future to have complete cyber understanding.
The goals and gaps outlined above apply to vehicle-based networks, in addition to command post networks. The Department of Defense (DoD) is currently making major efforts to develop comprehensive “standards-based communication” for these platforms, such as the U.S. Army’s Vehicular Integration for C4ISR/EW Interoperability (VICTORY) initiative. While the resulting standards help improve interoperability, data bus functionality and messaging services within ground vehicles, there are few solutions to the challenges involved in configuring and managing the overall theater and battlefield networks that connect all the platforms and warfighters.
Comms Management Challenges
 Addressing Communications Management Challenges.
Addressing Communications Management Challenges.
Today’s deployable comms teams use “best of breed” solutions, including a large number of satellite and radio technologies from multiple vendors. These teams have to deal with multiple vendor user interfaces, extensive training requirements, complex and error-prone configuration and long setup times. Associated with these challenges was the need for multiple IT professionals to deploy in the field, and high training expense for users.
NetOps and Cyber SA demand rapid and continuous innovation to meet evolving threats to DoD information dominance, as well as to address the key challenges that program managers and technical operations personnel face with network management, including:
• DoD overwhelmed by NetOps tools: Achieving its strategic vision for network management requires DoD to address the proliferation of NetOps tools. By some estimates, one DoD organization alone is using more than 140 NetOps tools, and in some cases, these solutions are duplicative. Simplifying network management requires a more unified, intuitive experience that has not existed in the past. At the same time, these tools should leverage open standards able to deliver a common look and feel. so that new capabilities can be easily integrated and used with minimum training.
• Staffing and Training: The volume and sophistication of tools require network specialists capable of managing networks. These specialists are difficult to recruit, train, and retain.
• Pace of innovation: DoD is excelling at rapidly fielding high-impact technology and leveraging the pace of innovation from the commercial sector. The flip side is that rapid adoption of new network technologies creates integration challenges and increases the network management learning curve. No one network vendor has all of the solutions, which results in the use of multiple user interfaces and disparate tools that drive up complexity.
• Expanded network: Increased automation to manage network operations and manage cyber vulnerabilities is required as networks and their attack surfaces grow with the addition of more sensors and IoT devices.
Network Management Solutions for NetOps + Cyber SA Requirements
Network management solutions that unify NetOps and Cyber SA capabilities should be able to deliver on several key requirements:
• Use open or industry-recognized standards for network management and data storage; examples include, but are not limited to, Simple Network Management Protocol (SNMP), Secure Shell (SSH), flow data, logging (SYSLOG), JSON, SOAP)
• Provide a configurable GUI (drag/drop, drop-down menus, etc.), visual map of network and services
• Provide visual fault indication with context available surrounding the fault (location, device, interface, service, IP, etc.)
• Provide configuration management functions (baseline, backup, and alerts of configuration change)
• Provide the ability to assess the security posture of network devices and remediate deficiencies (i.e.. OS versioning, deviation from a previously determined security template)
• Work in a hierarchical model construct (company, brigade, battalion, etc.) which can be configured to restrict or delegate read/write functions of the tool
Automating NetOps and Cyber SA
Fulfilling the vision of converging NetOps requires a solution that offers the ability to view the entire network through a single pane of glass while sharing access with deployed operators at any echelon. Such a solution should provide the following benefits:
• Ease and Speed Setup Time — Provide an intuitive user interface, making communications set-up and operation quick, easy to learn, and recall. Solutions should include customizable user interfaces and roles-based access control — with tailorable access to features, depending on user experience level — to reduce training time and costs.
• Reduce Configuration Errors — Significantly reduce configuration errors and assist organizations to maintain uptime, performance, and compliance with cybersecurity requirements.
• Simplify Troubleshooting — Simplify troubleshooting through integrated tools for both entry-level and advanced network administrators, to reduce reliance on contract Field Service Reps.
• Save Time — Automate complex, time consuming and error-prone tasks with powerful wizards, using common user interfaces across hardware and software components.
• Provide Cyber Situational Awareness — Deliver enhanced network and cyber SA at the core and edge of the network with extensive real-time status, alerts, and auditing.
• Facilitate Remote and Distributed Management — Facilitate remote management with the ability to monitor and change device configurations and troubleshoot from anywhere in the world.
• Streamline Innovation – Interoperate with a broad range of the most popular tactical and enterprise communications hardware, systems, and protocols- to streamline upgrades and adoption of new COTS technologies at the edge of the battlefield.
• Field Proven — Reduce acquisition risk because widely deployed, proven, and certified for DoD use.
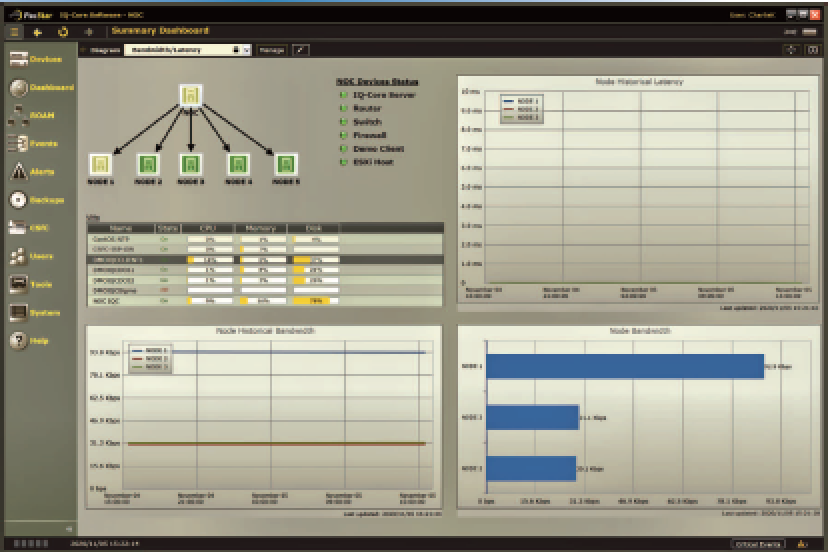
An example of a single pane of glass solution for managing and automating NetOps and Cyber SA that is available today is provided by Curtiss-Wright’s PacStar IQ-Core Software. This software, which is currently being integrated into the Army’s tactical network, addresses the growing problem of communication system management complexity.

IQ-Core Software is a comprehensive secure-communications management software that is designed to manage enterprise mobility solutions, tactical networks, and remote communications solutions, including supporting operations in disconnected, intermittent, and limited environments.
pacstar.com/
Charlie Kawasaki joined PacStar in early 2005 to lead the company’s technology strategy and future product roadmap for its proprietary product lines. Charlie current leads PacStar strategic initiatives – investigating and developing new integrated solutions and technologies to meet customer needs, in particular, focused on areas such as Commercial Solutions for Classified (CSfC), Cybersecurity, and Edge Computing. Charlie works closely with technology and product teams from our largest partners to create joint solutions, leveraging PacStar core technologies to create optimal tactical and expeditionary solutions. Charlie also serves as a technical and product evangelist raising awareness for PacStar solutions in our target markets and customers.
Charlie has extensive experience in product development, software engineering, technology licensing, patent development, business development, product marketing, general management and M&A. Charlie has over 35 years experience in early stage technology companies, creating dozens of software products for Internet infrastructure, cybersecurity, PC management, and relational databases. Charlie served as CEO of RuleSpace, Inc., which created AI-based Internet parental controls applications used by companies such as AOL, Yahoo and Microsoft. Before RuleSpace, he held product development and engineering management roles at companies including The Palace, Inc., Creative Multimedia Corp., Central Point Software, Inc., Asymetrix Corp. and Microrim, Inc. In 2019, he was named Outstanding Industry Collaborator by Oregon State University.

